ERPs Show Stock, Not Truth: Why Inventory Data Is No Longer Reliable
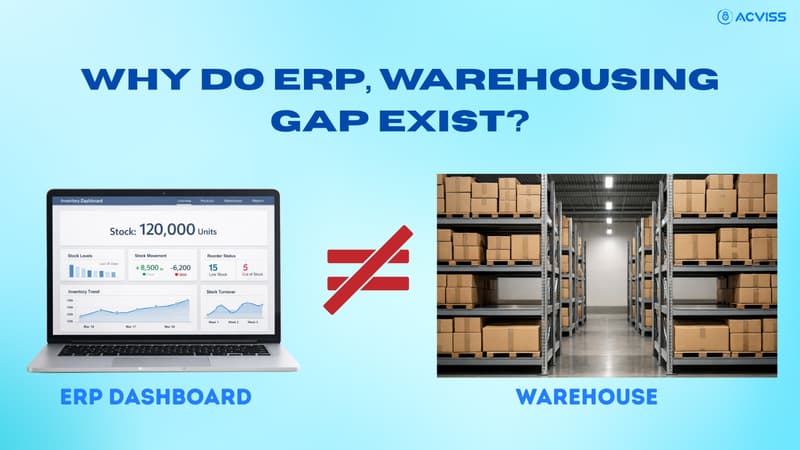
For decades, the ERP system has been treated as the ultimate source of operational truth. If the dashboard shows 120,000 units in stock, leadership assumes 120,000 genuine units are available. If serial numbers appear properly recorded, finance trusts the numbers. If dispatch entries are completed, sales forecasts move forward confidently.
Yet across industries, an uncomfortable pattern is emerging. The ERP shows stock. It does not show truth.
Inventory data accuracy is deteriorating in modern supply chains, not because systems are weak, but because the environment has changed. Counterfeit injection, channel diversion, ghost inventory, duplicate serial codes and warranty fraud now operate within the blind spots of traditional ERP architectures.
ERP inventory reliability was designed for transactional consistency. It was never built for authenticity verification.
That distinction now matters more than ever.
ERP Tracks Transactions, Not Authenticity
An ERP records what is entered into it. It tracks purchase orders, goods receipts, stock transfers and invoices. It logs transactions faithfully and performs arithmetic with precision.
What it cannot do is verify whether the physical product moving through the supply chain is genuine, duplicated, diverted or replaced.
Consider this.
When 10,000 units are received into a warehouse and logged into the ERP, the system assumes that those units correspond exactly to authorised production. It does not ask:
Are these products authentic?
Has any unit been replaced in transit?
Were additional unauthorised units inserted?
Are the serial numbers unique or duplicated?
ERP blind spots begin where authenticity begins.
In industries such as pharma, where product safety and serialisation compliance are tightly regulated, this gap is especially dangerous. A system that tracks quantities but cannot validate item-level authenticity exposes brands to compliance risk and reputational harm.
The Blind Spots in Inventory Data
Modern supply chains are complex, multi-tier and globally distributed. Within this complexity, several structural vulnerabilities thrive.
Counterfeit Injection
The OECD estimates that counterfeit goods represent more than 3 per cent of global trade. Counterfeits in supply chain scenarios often involve unauthorised products being introduced at distributor or dealer levels.
If counterfeit units enter the channel but are recorded as legitimate stock, the ERP reflects accurate quantities but an inaccurate reality.
Inventory data accuracy collapses because authenticity is assumed rather than validated.
Channel Diversion
Channel diversion detection is one of the least discussed yet most financially damaging blind spots.
Products intended for one region are diverted to another where pricing differs. ERP records may show legitimate transfers, yet unauthorised rerouting can distort margins and damage brand positioning.
Without scan-based inventory tracking and item-level authentication, diversion remains invisible.
Ghost Inventory
Ghost inventory occurs when stock exists in the system but not in physical reality. It may arise from shrinkage, miscounts or internal leakages.
Research across retail and manufacturing sectors suggests that inventory inaccuracy can range from 8 to 15 per cent in certain environments.
The ERP shows stock on paper. The warehouse shelves tell a different story.
Duplicate Serial Codes
In sectors like automotive spare parts authentication and medical device traceability, duplicate serial numbers pose serious risks.
ERP systems can record serials, but they do not inherently validate uniqueness across distributed networks. If duplicated codes appear in different regions, the ERP may not detect the anomaly unless an independent verification layer exists.
Warranty and Loyalty Fraud
Warranty claims and loyalty programmes rely heavily on serial verification.
If counterfeit or diverted products carry copied serial numbers, fraudulent claims increase. ERP systems record the claim transaction. They cannot confirm whether the unit is authentic.
This directly affects brand protection, customer satisfaction and financial stability.
Manual Reconciliation vs Real-Time Verification

Many organisations rely on periodic audits and reconciliations to maintain supply chain data integrity.
Quarterly stock counts. Annual audits. Random dealer inspections.
These methods worked in slower, less complex supply chains. They struggle in modern ecosystems.
Large multi-tier distribution networks move products rapidly across regions. By the time discrepancies are detected through manual reconciliation, the damage has already occurred.
Manual processes are:
Reactive rather than proactive
Labour-intensive
Prone to human error
Limited in scope
Real-time product verification shifts the model from delayed detection to immediate validation.
Instead of reconciling after discrepancies emerge, scan-based inventory tracking validates authenticity and movement at each transaction point.
From Visibility to Verification
For years, digital transformation efforts focused on visibility. Dashboards improved. Reports became real-time. Analytics became sophisticated.
Yet visibility without verification is incomplete.
Zero-trust supply chain architecture is now gaining relevance. The principle is simple. Trust nothing without validation.
In inventory management, this translates to:
Item-level authentication
Real-time product verification
Continuous scan-based validation
A product should not be assumed genuine because it exists in the ERP. It should be validated through product authentication technologies.
This shift moves organisations from quantity-based control to authenticity-based control.
The ERP + Authentication Layer Model

ERP systems remain essential. They coordinate finance, procurement, manufacturing and distribution.
However, they require augmentation.
An authentication layer introduces ground-truth intelligence. It verifies each unit independently of ERP transaction logs.
When integrated with non-cloneable security codes and blockchain traceability frameworks such as Origin by Acviss, inventory systems evolve beyond simple recording mechanisms.
Origin enables immutable track and trace solutions across the supply chain. Each transaction is recorded transparently, creating an auditable chain of custody.
When products carry unique, non-replicable digital identities, real-time verification becomes possible at:
Manufacturing
Warehouse intake
Distributor handover
Dealer sale
Warranty activation
ERP synchronisation with this authentication layer creates a hybrid model.
The ERP tracks transactions.
The verification layer validates truth.
Industry-Specific Impact
Pharma Serialisation Compliance
Pharma serialisation compliance demands unit-level traceability. Regulatory frameworks require product traceability from manufacturer to patient.
Without item-level authentication, compliance becomes fragile. Counterfeit injection can undermine product safety and invite regulatory penalties.
Authentication-driven track and trace solutions strengthen both regulatory readiness and IP protection.
Automotive Spare Parts Authentication
Counterfeit spare parts compromise vehicle safety and brand integrity.
ERP systems can record shipments. They cannot detect if counterfeit parts have entered secondary markets with duplicated serial numbers.
Scan-based inventory tracking combined with non-cloneable identities strengthens trademark protection and brand authentication.
FMCG Distribution Leakage
FMCG distribution leakage erodes margins quietly.
Diversion across regions affects pricing discipline. Ghost inventory creates stock planning errors.
Real-time verification improves supply chain management and enhances customer engagement by ensuring authentic product availability.
Medical Device Traceability
Medical device traceability is directly linked to patient safety.
Duplicate serial codes or counterfeit components pose serious risks. An authentication layer supports product verification and strengthens compliance documentation.
The Financial Cost of Inaccurate Inventory Data
Inventory distortion impacts more than operations.
It affects:
Revenue forecasting
Working capital allocation
Compliance reporting
Insurance claims
Investor confidence
If ERP inventory reliability is compromised, financial statements reflect inaccurate asset valuations.
Inventory accuracy is not an operational metric. It is a financial integrity metric.
Building a Zero Trust Supply Chain

A zero-trust supply chain does not assume that products are genuine simply because they are recorded.
It validates every unit.
Core components include:
Non-cloneable security codes
Scan-based inventory tracking
Real-time discrepancy detection
Continuous product verification
This model transforms supply chain management from reactive control to proactive assurance.
Brand verification becomes embedded within operational workflows rather than treated as an afterthought.
The Strategic Imperative
Supply chains are no longer linear. They are networked, global and digitally exposed.
Counterfeiting in supply chain activity continues to evolve. Channel diversion detection requires intelligence beyond transactional logs. Ghost inventory undermines planning accuracy.
ERP blind spots cannot be resolved through additional reporting alone.
They require structural change.
Integrating authentication-driven track and trace solutions with ERP systems builds a resilient integrity model. It protects trademarks, strengthens IP protection and enhances product safety.
Most importantly, it restores trust in inventory data.
Reclaiming Ground Truth in Inventory Systems
The ERP was never designed to validate authenticity. It was built to record transactions efficiently.
As supply chains grow more complex, that design limitation becomes visible.
Organisations that continue relying solely on ERP dashboards risk misinterpreting stock data as operational truth.
Inventory data accuracy now depends on verification.
By combining ERP infrastructure with item-level authentication, non-cloneable security codes and blockchain-backed traceability frameworks such as Origin, businesses can move from assumed accuracy to verified integrity.
The future belongs to organisations that understand this distinction.
Interested to learn more? Get in touch with us to explore how authentication-driven verification layers can strengthen ERP inventory reliability, enhance brand protection and build a truly zero-trust supply chain.