How to Find Out If Dark Web Is Selling Your Brand
Search engines have become the default lens through which most brand protection teams monitor risk. If it appears on Google, it is considered visible, traceable, and actionable. If it does not, it is often assumed to be marginal.
That assumption is increasingly flawed.
A parallel economy exists beyond indexed websites, one that operates with its own rules, marketplaces, and buyer networks. This is where counterfeit goods are quietly traded, where packaging templates are sold as digital assets, and where authentication systems are studied, tested, and sometimes bypassed. This is the dark web, and for brand owners, it is no longer optional to understand it.
This article examines what is actually happening beneath the surface, why conventional monitoring fails, and how dark web intelligence can be turned into meaningful action.
What the Dark Web Really Is and Why It Matters to Brand Protection
The dark web is often misunderstood. It is not a vast, chaotic underworld filled with sensational threats. In reality, it is a small segment of the internet, estimated to account for less than one per cent of total content. Yet its importance lies not in size, but in function.
It provides anonymity, decentralisation, and access to a global network of buyers and sellers who prefer to operate outside regulated channels.
From a brand protection perspective, the dark web serves three key roles:
A wholesale marketplace for counterfeit goods
A distribution channel for intellectual property and packaging assets
A knowledge hub where methods to bypass product authentication and product verification systems are exchanged
Research spanning 2014 to 2025 shows that counterfeit goods account for approximately 1.5% to 2.69% of all darknet listings. While this appears small, the trade is highly specialised and persistent.
More importantly, it is structurally different from what enforcement teams see through seizures or marketplace monitoring.
What Is Actually Being Sold: Separating Myth from Operational Reality
The popular narrative around the dark web often focuses on extreme or sensational content. For brand owners, this is largely irrelevant.
What matters is the operational layer of commerce.
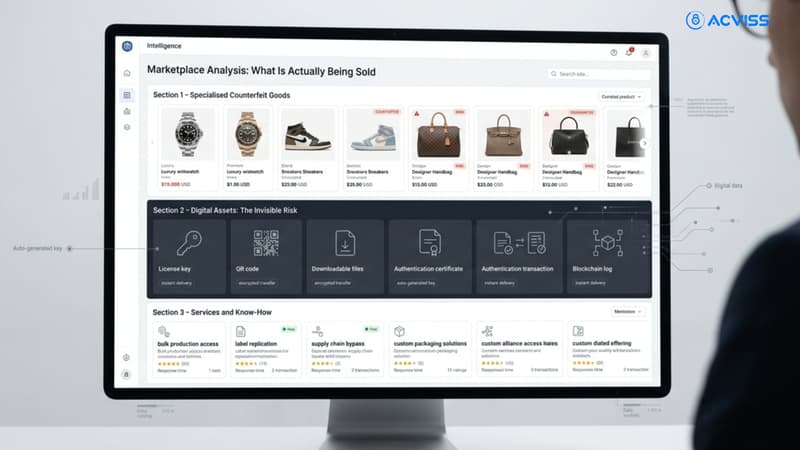
1. Specialised Counterfeit Goods
The dark web does not mirror the bulk counterfeit trade seen at ports and borders. Instead, it prioritises high-value, low-volume products.
Watches account for nearly 60% of listings and over 68% of sales volume
Clothing, sunglasses, and electronics follow at significantly lower shares
Pharmaceuticals and high-risk goods appear in niche but critical segments
These products are often shipped as individual parcels rather than large consignments, making them harder to detect through traditional supply chain managementcontrols.
2. Digital Assets: The Invisible Risk
Beyond physical goods, a growing category involves digital components of counterfeiting:
Label and packaging templates
Hologram replication guides
QR code structures and cloning techniques
Documentation used for trademark protection evasion
This is where IP protection risks intensify. A counterfeit product can be reproduced anywhere once its design assets are available.
3. Services and Know-How
Some vendors do not sell products at all. They sell knowledge.
This includes:
Guides to bypass product traceability systems
Methods to exploit weak points in track and trace implementations
Techniques to manipulate customer-facing verification interfaces
For brands investing in anti-counterfeiting solutions, this represents a direct and evolving threat.
The Economics of Counterfeiting on the Dark Web
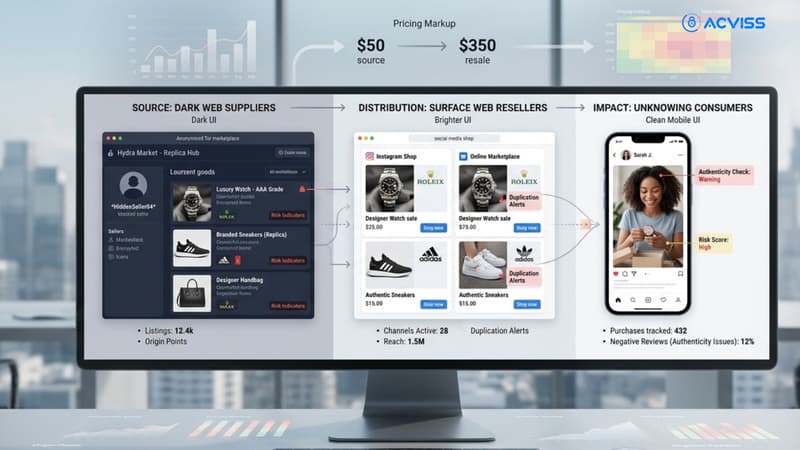
Understanding pricing and incentives is essential to interpreting risk.
Dark web counterfeit goods are typically priced at one-third of the genuine product value. Digital goods may be sold for as little as one-sixth of their original price.
This creates a powerful arbitrage opportunity.
A counterfeit watch purchased on the dark web can be resold on the surface web at dramatically higher prices. In some cases, surface web listings for similar items are over 140 times more expensive than their dark web counterparts.
This pricing gap fuels a layered ecosystem:
Dark web suppliers
Surface web resellers
Unknowing consumers
The result is a supply chain that blends illicit and legitimate channels, complicating product safety and customer satisfaction outcomes.
Why Conventional Monitoring Tools Fail
Most online brand monitoring tools rely on indexed content. They scan marketplaces, social media platforms, and websites that are accessible through standard browsers.
The dark web operates differently.
Limited Accessibility
Dark web marketplaces require specialised browsers and access protocols. They are intentionally designed to avoid indexing.
Fragmented Marketplaces
Following law enforcement actions such as the takedown of major platforms like AlphaBay, the ecosystem has shifted.
Instead of large centralised markets, activity is now distributed across:
Smaller niche marketplaces
Invitation-only forums
Single-vendor shops
This fragmentation makes detection significantly harder.
Encryption and Anonymity
Transactions are conducted using cryptocurrencies and encrypted communication channels. Vendor identities are masked, and listings frequently omit critical details such as origin.
Over 20% of listings leave shipping origins undeclared, further complicating investigation.
What Effective Dark Web Counterfeit Monitoring Looks Like
Monitoring the dark web requires a different approach. It is not an extension of search engine monitoring but a distinct capability.
Effective dark web counterfeit monitoring involves:
Continuous Intelligence Gathering
Rather than periodic scans, monitoring must be ongoing. Marketplaces appear and disappear frequently, and vendor behaviour evolves rapidly.
Contextual Analysis
Raw listings are not enough. Intelligence must be interpreted.
For example:
A single listing may indicate experimentation
Multiple listings across vendors may signal organised supply
Repeated mentions of a brand may indicate targeted counterfeiting
Cross-Channel Correlation
Dark web findings must be linked with surface web activity.
A product appearing on a marketplace may later surface on e-commerce platforms, social media, or grey markets.
Without correlation, insights remain isolated and underutilised.
Interpreting Dark Web Intelligence: Signal vs Noise
One of the most common mistakes in brand protection dark web initiatives is overreacting to isolated findings.
Not every listing represents an immediate threat.
Indicators of Intent
Prototype listings
Discussions around product feasibility
Requests for supplier contacts
These indicate interest but not necessarily active distribution.
Indicators of Active Supply
Multiple listings across vendors
Established vendor ratings and transaction histories
Detailed product descriptions and shipping options
These signals suggest operational counterfeiting networks.
Distinguishing between these states is critical for prioritising response.
What to Do Once You Have Intelligence
Dark web intelligence is only valuable if it leads to action.
Supporting Law Enforcement
Structured intelligence can assist investigations by:
Identifying high-risk vendors
Mapping geographic origins
Highlighting emerging trends
Dark web data has increasingly become a cost-effective complement to traditional enforcement methods.
Strengthening Supply Chain Controls
Insights into origin points and distribution methods can inform track and trace strategies.
For example:
Increased monitoring of parcel shipments
Reinforcement of vulnerable nodes in product traceability systems
Enhanced verification at distribution points
Improving Product Authentication
If counterfeiters are studying or bypassing existing systems, brands must evolve their defences.
This includes:
Enabling real-time product verification
Integrating consumer-facing authentication mechanisms
Without strong product authentication, even the best intelligence cannot prevent counterfeit penetration.
The Risks of DIY Dark Web Monitoring
Attempting to monitor the dark web without expertise carries significant risks.
Legal Exposure
Engaging with illicit marketplaces, even passively, may violate jurisdictional laws or expose organisations to regulatory scrutiny.
Operational Risks
Inexperienced monitoring can:
Misinterpret data
Engage with malicious actors
Trigger retaliation or exposure
Security Threats
Dark web environments often contain malware, phishing traps, and surveillance mechanisms.
Without secure infrastructure, monitoring efforts can compromise internal systems.
Integrating Dark Web Monitoring into a Broader Brand Protection Strategy

Dark web intelligence should not operate in isolation. It must be part of a multi-layered approach.
Layer 1: Surface Web Monitoring
Tracking counterfeit listings on marketplaces, social platforms, and websites.
Layer 2: Dark Web Intelligence
Identifying upstream supply, digital assets, and emerging threats.
Layer 3: Product Authentication
Ensuring that every product can be verified by stakeholders, including consumers.
Layer 4: Supply Chain Visibility
Implementing track and trace and product traceability systems to monitor movement and detect diversion.
Layer 5: Consumer Engagement
Educating customers on verification processes to enhance customer satisfaction and trust.
Together, these layers create a resilient anti-counterfeiting solution.
The Role of Technology in Closing the Gap
Technology is central to modern brand protection solutions.
AI-driven systems can analyse vast datasets, identify patterns, and detect anomalies across both surface and dark web environments.
Truviss by Acviss, positioned as an online anti-counterfeiting platform, demonstrate how digital intelligence can be operationalised. By scanning domains, marketplaces, and hidden networks, such systems extend visibility beyond conventional monitoring.
However, detection alone is not sufficient.
Without brand authentication and product verification mechanisms at the product level, counterfeit goods will continue to circulate.
This is particularly critical in sectors such as:
Pharma, where counterfeit products directly impact patient safety
Premium FMCG, where trust defines brand value
Electronics, where performance and safety are closely linked
A Changing Landscape That Demands Attention
The dark web is not replacing traditional counterfeit channels. It is augmenting them.
It serves as:
A sourcing layer for counterfeit goods
A distribution channel for IP assets
A coordination hub for illicit networks
Ignoring it does not reduce risk. It simply reduces visibility.
Brands that rely solely on surface web monitoring are operating with incomplete intelligence.
Securing the Digital Presence
Counterfeiting has evolved from a physical supply chain problem into a hybrid digital ecosystem. The dark web sits at the centre of this transformation, quietly enabling trade, knowledge exchange, and distribution at a global scale.
Effective dark web brand protection requires more than awareness. It demands specialised monitoring, contextual intelligence, and integration with broader brand protection, IP protection, and anti-counterfeiting solutions.
Most importantly, it requires a shift in mindset.
Visibility is no longer limited to what can be searched. It must extend to what is deliberately hidden.
Brands that recognise this early will be better positioned to protect their products, their customers, and their reputation.
Interested in learning more about how to strengthen your brand protection strategy across both surface and dark web channels? Get in touch with us.